A fresh dump of leaked CIA documents by WikiLeaks has revealed how the spy agency used compromised flash drives to infiltrate air-gapped networks.
The documents [pdf], dated between August 2012 and February 2016 and part of WikiLeaks' Vault 7 trove of files, show the CIA created a "custom covert network" within infected networks to conduct surveillance.
The so-called Brutal Kangaroo toolkit used compromised Windows PCs to spread malware to non-networked machines via USB sticks.
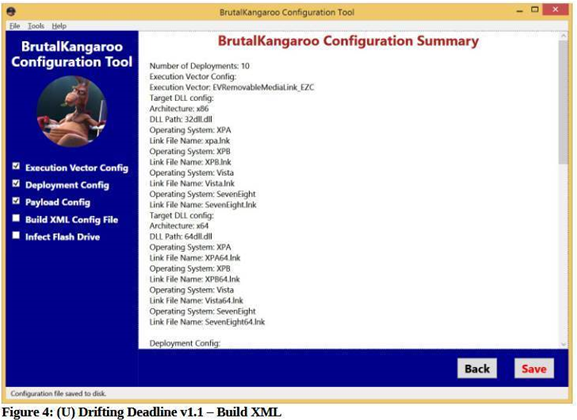
Brutal Kangaroo contains four key tools: the main Drifting Deadline GUI-based builder that generates malware; the Shattered Assurance server-side code that runs on infected machines and automates the infection of USB drives; the Shadow tool used to manage multiple infected computers on an air-gapped network; and the Broken Promise data exfiltration and examination tool.
To execute a successful attack, operatives first need to infect a Windows internet-connected computer at their target organisation with the Drifting Deadline malware.
Once a USB is inserted into the compromised machine, it is similarly infected with the malware by the Shattered Assurance code.
The compromised USB stick infects its ultimate target when it is used on an air-gapped machine.
Once an infection has been achieved on an air-gapped computer, the Shadow tool will look for other connected systems and infect them.
Shadow can be set up to collect as much as 10 percent of the system's memory data. It stores the data it collects on an encrypted partition of the victim computer's hard drive.
However, several antivirus products from the likes of Avira, Bitdefender, Symantec, and Rising Antivirus are now able to detect Brutal Kangaroo malware.
Microsoft has also since patched the LNK file handling flaws used by the CIA in its Brutal Kangaroo attacks, one as recently as last week.
WikiLeaks first revealed the existence of Brutal Kangaroo in March, but with limited details on how it operates. Today's dump offers a detailed user guide on the toolkit.



















