A new malware strain called IOCONTROL has emerged, posing a significant threat to Internet of Things (IoT) devices and operational technology (OT) systems, particularly those in critical infrastructure.
First observed in December 2024, IOCONTROL is allegedly created by the anti-Israeli and pro-Iranian hacktivist group “Cyber Av3ngers.”
Technical Analysis Reveals Sophisticated Capabilities
IOCONTROL employs advanced techniques to evade detection and establish persistence on targeted systems.
The malware uses executable packing with modified UPX magic values, making it challenging to identify and unpack.
Once unpacked, it creates multiple environment variables using the setenv() function, with values derived from a hard-coded GUID string.

The malware establishes persistence by creating directories with full permissions and copying itself to /usr/bin/iocontrol.
It then writes a bash script that runs at system startup, containing watchdog and cleanup code.
IOCONTROL’s communication with its command and control (C2) server involves a DNS lookup process using CloudFlare, followed by connection establishment via the MQTT protocol.
According to Flashpoint, this streamlined networking protocol is particularly suited for IoT devices with limited processing capabilities.
Threat Actor Objectives and Potential Impact
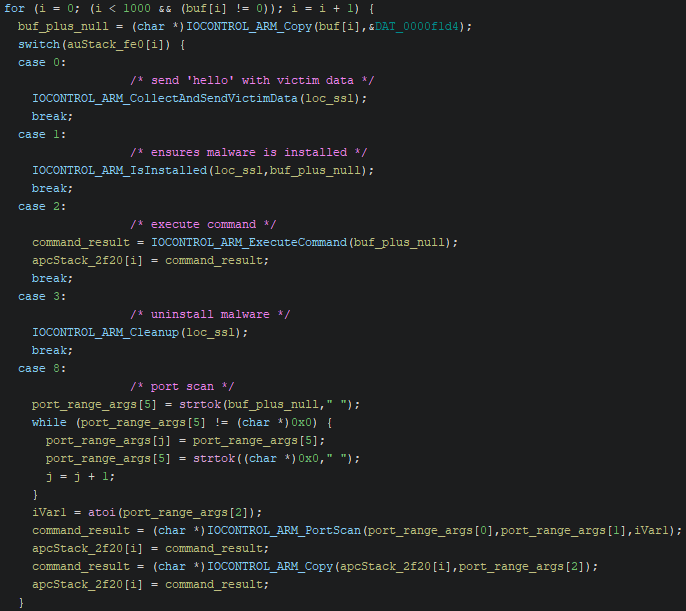
Once installed, IOCONTROL enables threat actors to achieve multiple objectives, including:
- Remote access and control of infected systems.
- System manipulation.
- Data exfiltration.
- Lateral movement within networks.
- Surveillance of compromised infrastructure.
The malware’s ability to execute system commands allows attackers to perform more dangerous activities, such as loading additional payloads or damaging critical systems.
IOCONTROL’s emergence highlights the growing sophistication of threats targeting IoT and OT environments.
Its alleged attribution to Cyber Av3ngers and potential availability for sale on underground forums suggest that this malware could see increased use in future attacks.
Organizations, particularly those managing critical infrastructure, are advised to enhance their defenses against such evolving threats.
Implementing robust IoT and OT security measures, along with comprehensive threat intelligence, will be crucial in mitigating the risks posed by IOCONTROL and similar malware strains.
Are you from SOC/DFIR Teams? – Analyse Malware, Phishing Incidents & get live Access with ANY.RUN -> Start Now for Free.
.webp?w=696&resize=696,0&ssl=1)


