Security researcher Nick Cerne from Bishop Fox has published findings comparing malware development in Rust versus traditional C/C++ languages.
The research demonstrates how Rust provides inherent anti-analysis features that make malware more difficult to reverse engineer.
According to Cerne’s analysis, languages like Rust, Go, and Nim have become increasingly popular among malware authors for two primary reasons: increased difficulty in reverse engineering and improved evasion of signature-based detection mechanisms.
Technical Advantages of Rust-Based Malware
The research cites a 2023 study from Rochester Institute of Technology that confirmed several technical advantages of Rust for malware development.
Rust binaries are significantly larger than C/C++ equivalents, which increases reverse engineering complexity.
When comparing functionally identical shellcode loaders, the Rust version was 151.5 KB compared to just 71.7 KB for the C version.
More importantly, automated malware analysis tools produce more false positives and negatives when analyzing Rust-compiled malware.
Standard reverse engineering tools like Ghidra and IDA Free struggle with disassembling Rust binaries compared to C/C++ counterparts.
Cerne demonstrated this by examining decompiled Ghidra output from both languages. While C code was easily readable after decompilation, the Rust equivalent was significantly more complex due to rustc optimizations and differences in memory management.
According to the Report, these optimizations result in fewer clear function boundaries and highly optimized assembly that’s difficult to interpret.

Practical Demonstration with File Mapping Injection
The research included a practical demonstration of a Rust-based malware dropper that uses file mapping injection techniques to evade detection.
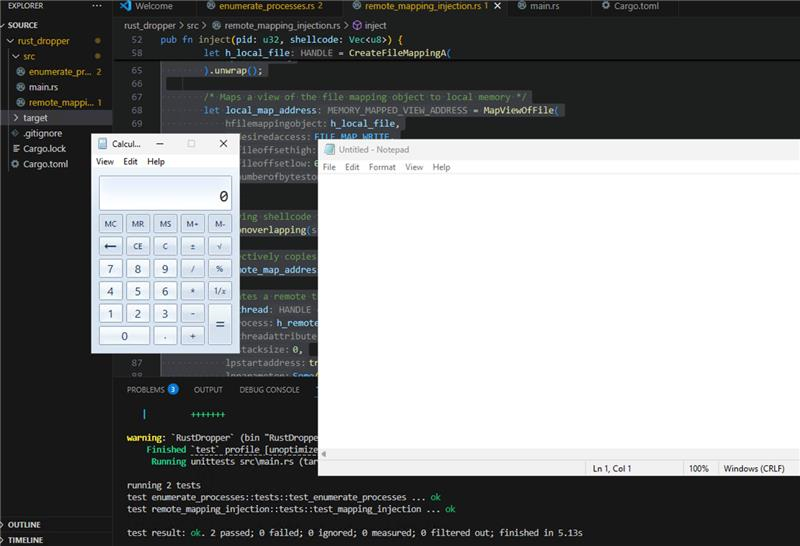
This approach leverages lesser-known Windows APIs like CreateFileMapping, MapViewOfFile, and MapViewOfFileNuma2 instead of commonly monitored functions like VirtualAlloc and VirtualAllocEx.
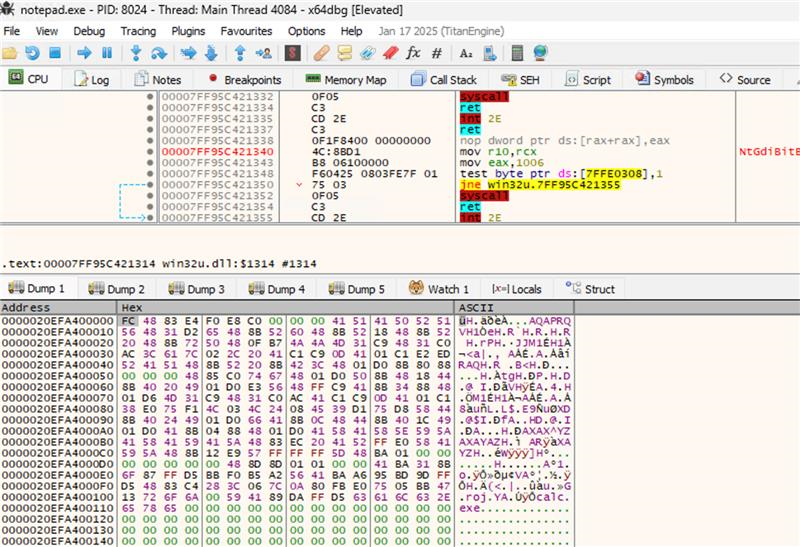
Cerne successfully demonstrated the technique by injecting shellcode that launches calc.exe into a notepad.exe process and later extended this to stage a Sliver C2 payload using HTTPS communication.
One notable OPSEC consideration is that Rust includes absolute file paths in compiled binaries for debugging purposes, potentially exposing identifying information about the development environment.
The findings suggest that as security solutions evolve, malware development continues to be a cat-and-mouse game requiring constant refinement of techniques, with Rust offering compelling advantages for those seeking to develop more evasive malicious code.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup – Try for Free
.webp?w=696&resize=696,0&ssl=1)


